Third-Party Risk Management
Managing Third-Party Risks in Banking Relationships
THIRD-PARTY RISK MANAGEMENT | US
Third-Party Risk Management – Principles, Elements and Best Practices
On June 2023, the Federal Reserve Board (FRB), the Federal Deposit Insurance Corporation (FDIC), and the Office of the Comptroller of the Currency (OCC), collectively the “Agencies,” issued final guidance on managing risks associated with third-party relationships (the “Guidance”).
The Guidance identified four (4) key principles: (1) supervisory reviews, (2) governance, (3) risk management, (4) third-party relationship life cycle. A successful third-party risk management program includes four (4) basic elements: (1) risk assessment, (2) due diligence, (3) contracts, and (4) oversight, which will help organizations build a solid strategy to identify and reduce risks of using third parties in their business operations. Whether an globally scaling growth company or Fortune 500, a third party risk management program is a continuous process and must be an integral part of the business.
Understanding System and Organization Controls (SOC) Reports
SOC | GLOBAL
The SOC Framework, the Comparison and the Different Types of SOC Reports
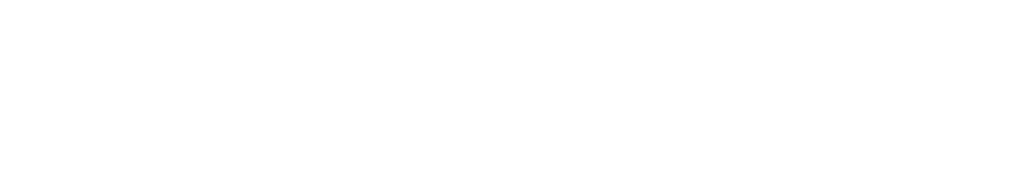
System and Organization Controls, formerly known as Service Organization Control (SOC) Reports for Service Organizations, help companies that provide services to other entities establish trust and confidence in their service delivery processes and controls. SOC Reports are the compiled result and findings of a SOC Examination, which is performed by independent Certified Public Accountants and designed to provide assurance over the functioning of an organization’s internal controls.
SOC is a suite of service offerings developed by The American Institute of CPAs (AICPA) for CPAs to use to evaluate system-level controls of a service organization or entity level controls of other organizations. These internal control reports about services provided by a service organization provide valuable information to serviced entities so they are able to assess and address risks associated with an outsourced service. SOC 2®: Trust Services Criteria (TSC) is the most common and expected report. It provides assurance to user entities that a service organization provides services securely relative to availability, confidentiality, processing integrity and privacy.
Other Relevant Spotlights
SANCTIONS | US
Geolocation is More Than Just a Postcode
A Spotlight on Geolocation and IP Address Screening to Maintain Compliance with the Office of Foreign Assets Control (OFAC)
CYBERSECURITY
The Understanding and Defending Against Social Engineering Attacks
A Spotlight on How You Can Protect Your Organization From Social Engineering Attacks
CYBERSECURITY
The Rise of Advanced Passwordless Authentication
A Spotlight on the Transition from Traditional Authentication to Passwordless Authentication Methods
415.352.1060 2193 Fillmore Street, Suite 1
San Francisco, CA 94115

RISK | STRATEGY | CYBER COMPLIANCE MANAGEMENT
© 2026 Stratis Advisory LLC. All Rights Reserved.
Terms of Use | Privacy Policy